Autenticação de dois fatores e multifator (2FA/MFA)
O FoxIDs suporta tanto um modo simples de dois fatores como um modo avançado de multifator no método de autenticação de login.
- Modo de dois fatores:
Advanced multi-factorestá desativado (predefinição). - Modo multifator:
Advanced multi-factorestá ativado.
Use o modo de dois fatores quando um fator adicional for suficiente. Use o modo multifator quando precisar de uma cadeia MFA ordenada ou quiser incluir métodos de autenticação como passos MFA.
Conceitos
A autenticação de dois fatores (2FA) e a autenticação multifator (MFA) adicionam um ou mais passos de verificação após o início de sessão primário.
- 2FA: um início de sessão primário mais um fator adicional.
- MFA: um início de sessão primário mais um ou mais fatores adicionais ordenados.
Fatores suportados
O FoxIDs suporta fatores incorporados e métodos de autenticação como itens MFA.
| Factor | Type | AMR value |
|---|---|---|
| Código SMS | Incorporado | sms |
| Código por email | Incorporado | email |
| Código de app autenticadora | Incorporado | otp |
| Código de recuperação | Incorporado (app autenticadora) | otp |
| Método de autenticação (OIDC, SAML 2.0, Environment Link) | Item configurável | AMR configurado, ou nome do método/perfil se vazio |
Pode usar qualquer app autenticadora compatível, por exemplo Google Authenticator, Microsoft Authenticator, Authy e outras apps TOTP.
Quando MFA é exigido
O MFA é acionado quando se aplica uma das seguintes condições:
- O utilizador tem
Require multi-factor (2FA/MFA)ativado. - O método de autenticação de login tem
Require multi-factor (2FA/MFA)ativado. - A aplicação que chama pede MFA com ACR
urn:foxids:mfa.
Os requisitos MFA aplicam-se em ambos os modos. Se Advanced multi-factor estiver desativado, o requisito é cumprido pelo fluxo simples de dois fatores.
Se forem pedidos valores ACR específicos juntamente com urn:foxids:mfa, apenas os valores ACR correspondentes são exigidos.
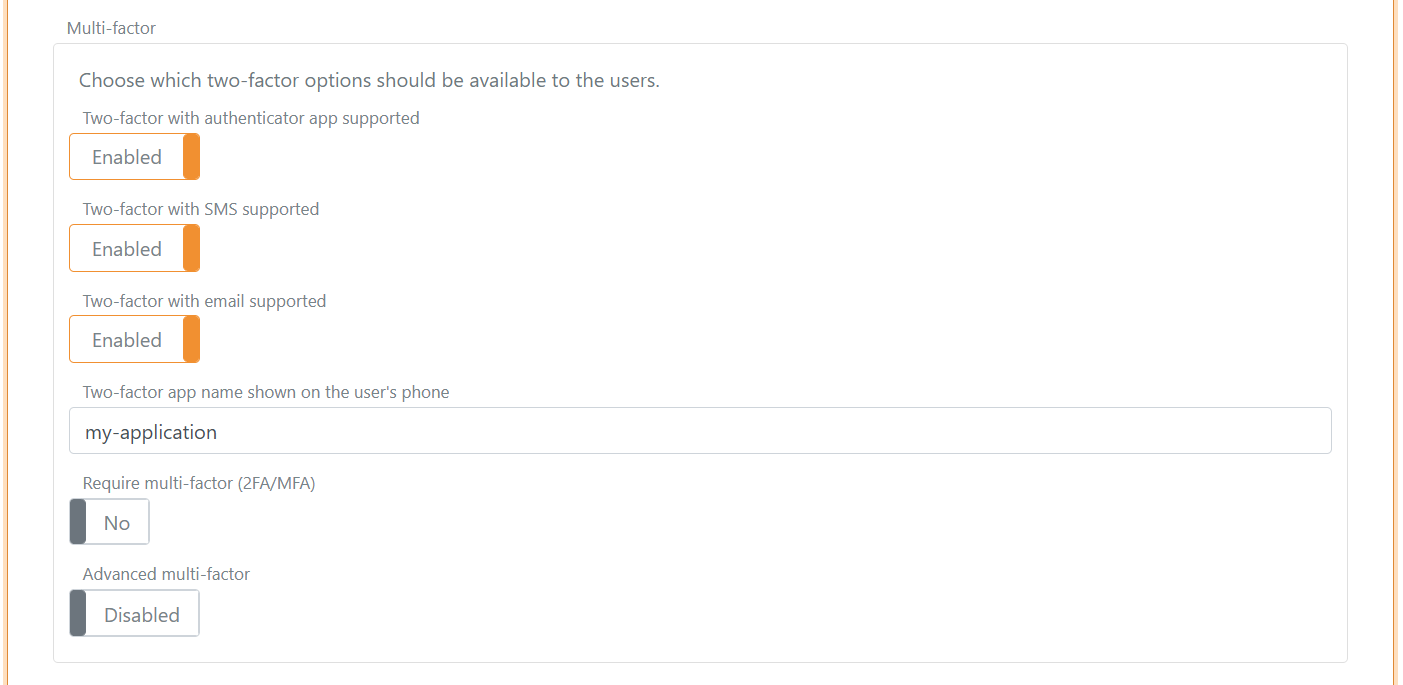
Modo de dois fatores (Advanced multi-factor está desativado)
Neste modo, as opções incorporadas de dois fatores são configuradas diretamente:
- App autenticadora
- SMS
Para configurar o modo de dois fatores:
- Abra o separador Authentication.
- Clique no método de autenticação Login para editar.
- Clique em Show advanced.
- Vá para a secção Multi-factor.
- Mantenha
Advanced multi-factordesativado e configure as opções App autenticadora, SMS e Email.
O nome da app autenticadora mostrado aos utilizadores pode ser configurado. Por predefinição, é usado o nome do tenant.
Os fatores SMS e email exigem informação de contacto do utilizador. Esta pode ser fornecida como identificadores de utilizador ou como claims (phone_number e email).
Comportamento de seleção de dois fatores
No modo de dois fatores, o FoxIDs prefere uma app autenticadora já registada. Se não houver nenhuma registada, o SMS tem prioridade sobre o email quando ambos estão disponíveis.
| SMS two-factor enabled and user has phone number | Email two-factor enabled and user has email | User has registered authenticator app | Possible two-factor type(s) | Selected two-factor type |
|---|---|---|---|---|
| false | false | false | Configuração da app autenticadora | Configuração da app autenticadora |
| false | false | true | App autenticadora | App autenticadora |
| true | false | false | SMS, com configuração opcional da app autenticadora após a verificação por SMS | SMS |
| true | false | true | SMS e app autenticadora | App autenticadora |
| false | true | false | Email, com configuração opcional da app autenticadora após a verificação por email | |
| false | true | true | Email e app autenticadora | App autenticadora |
| true | true | false | SMS e email, com configuração opcional da app autenticadora após verificação por SMS ou email | SMS |
| true | true | true | SMS, email e app autenticadora | App autenticadora |
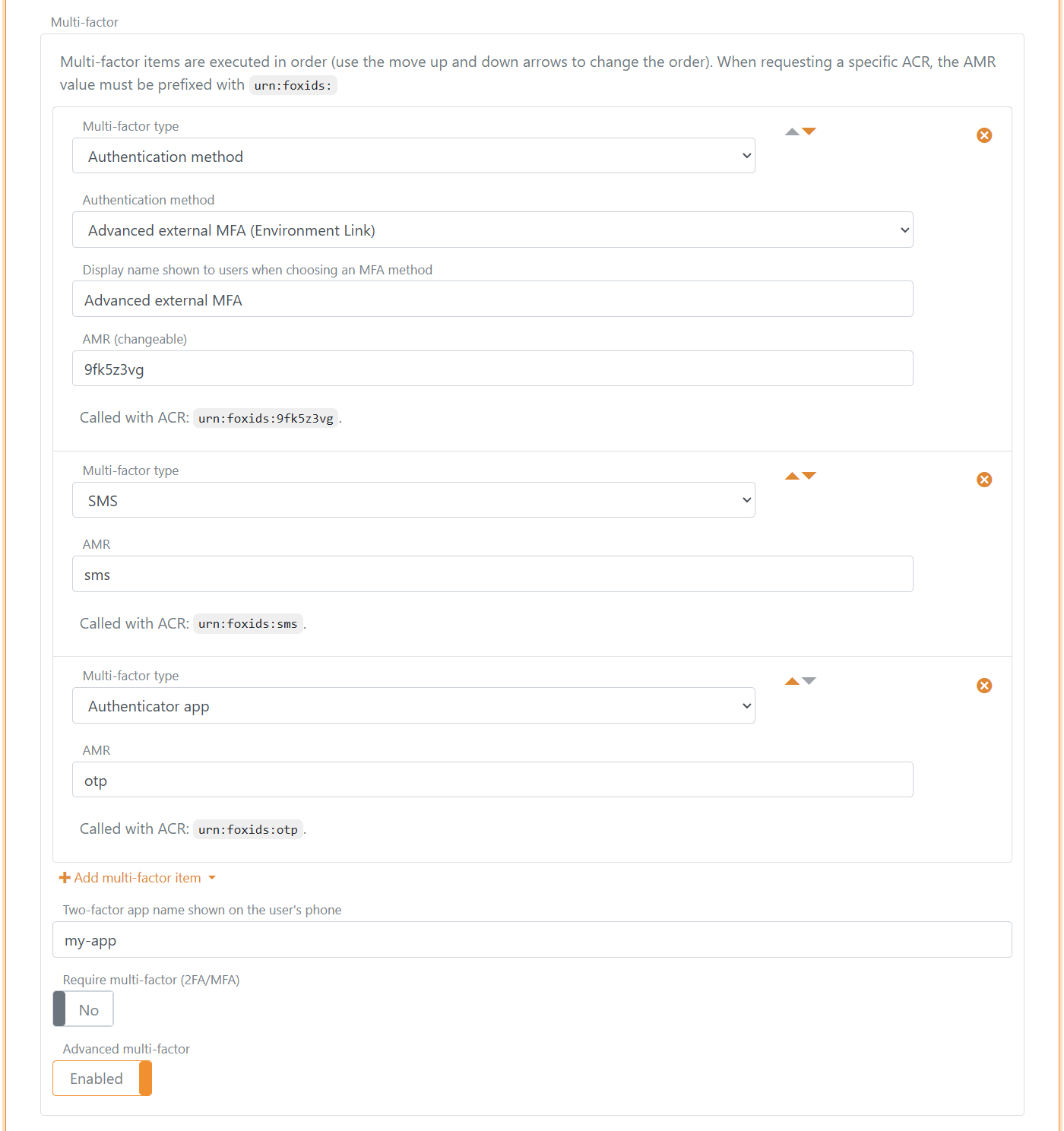
Modo multifator (Advanced multi-factor está ativado)
Quando Advanced multi-factor está ativado, o MFA é configurado como uma lista ordenada de até 5 itens MFA.
Para configurar o modo multifator:
- Abra o separador Authentication.
- Clique no método de autenticação Login para editar.
- Clique em Show advanced.
- Vá para a secção Multi-factor.
- Ative
Advanced multi-factore configure os itens MFA ordenados.
Tipos de item MFA suportados:
- Incorporados:
- SMS
- App autenticadora
- Método de autenticação:
Regras de configuração:
- Os tipos de item incorporados só podem ser configurados uma vez cada.
- Itens de método de autenticação podem ser configurados várias vezes, por exemplo com perfis diferentes.
- Os itens são executados pela ordem da lista.
- Pode adicionar, remover e reordenar itens.
Comportamento de AMR e ACR do item MFA
Cada item MFA concluído contribui com valores do claim AMR para a sessão.
- Os valores AMR incorporados são fixos:
- SMS:
sms - Email:
email - App autenticadora e código de recuperação:
otp
- SMS:
- AMR de item de método de autenticação:
- Pode ser configurado um AMR personalizado opcional.
- Se o AMR estiver vazio, é usado o nome do método de autenticação ou do perfil.
Os valores ACR pedidos são comparados com os valores AMR do item MFA neste formato:
urn:foxids:<amr>- Exemplo:
urn:foxids:link
urn:foxids:mfa é o requisito MFA geral, e o FoxIDs adiciona AMR mfa quando o MFA é concluído.
Seleção e encadeamento de itens MFA
- Se forem pedidos valores ACR específicos, um dos itens MFA correspondentes tem de ser concluído.
- Se apenas for pedido MFA geral, qualquer item MFA configurado e disponível pode cumprir o requisito.
- Se existir mais do que um item MFA elegível e o FoxIDs não conseguir selecionar um automaticamente, é mostrada uma UI de seleção.
- Se estiver configurada uma app autenticadora e esta já estiver registada, o FoxIDs dá-lhe prioridade para pedidos MFA gerais.
- Se a configuração da app autenticadora for selecionada e ainda não estiver registada, o fluxo de configuração pode continuar após um passo selecionado de SMS, email ou método de autenticação.
- Se apenas a app autenticadora estiver configurada, a configuração pode começar diretamente após o início de sessão do primeiro fator.
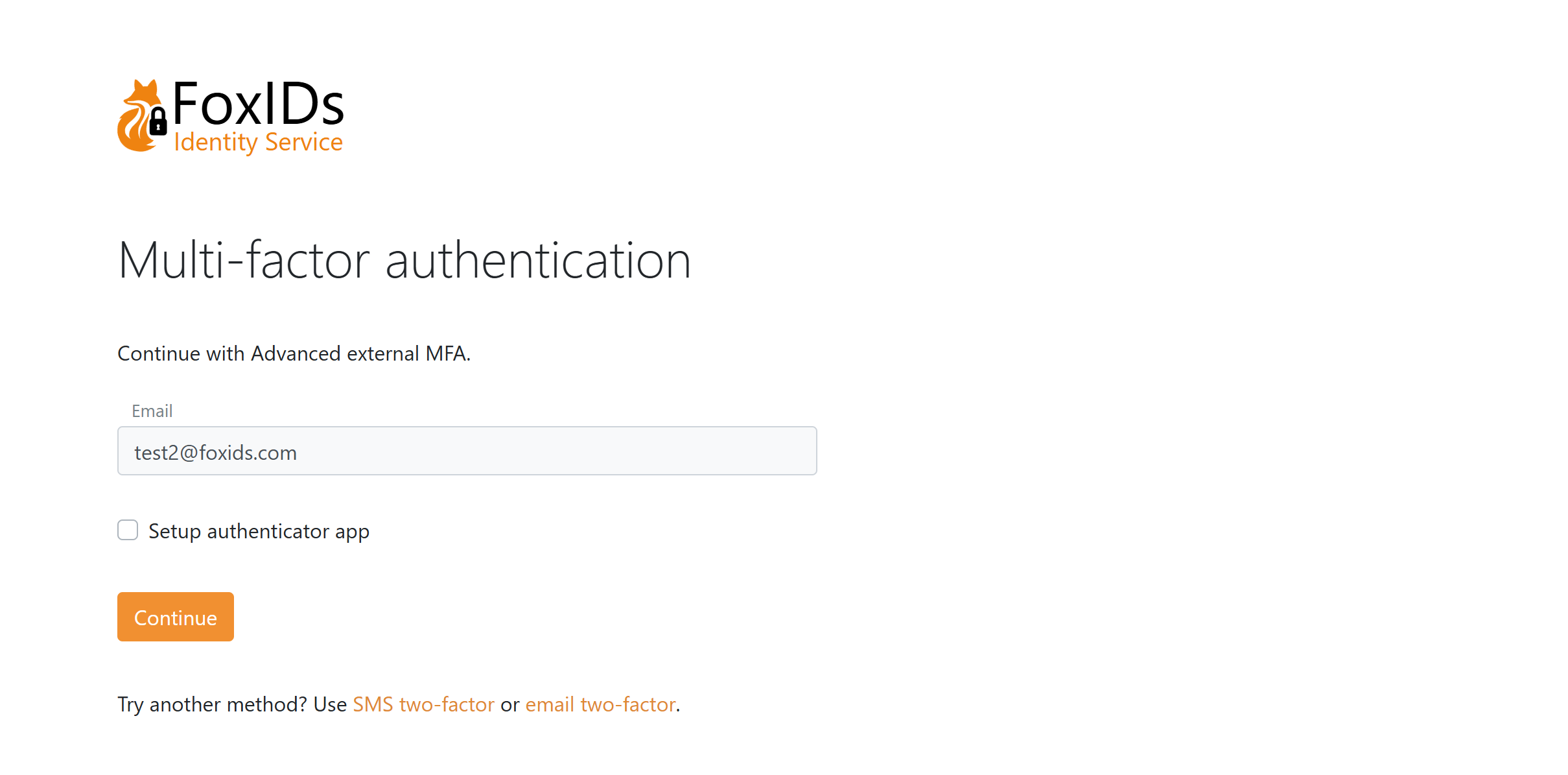
Página de método de autenticação MFA com registo opcional da app autenticadora e a opção de escolher um item MFA diferente.
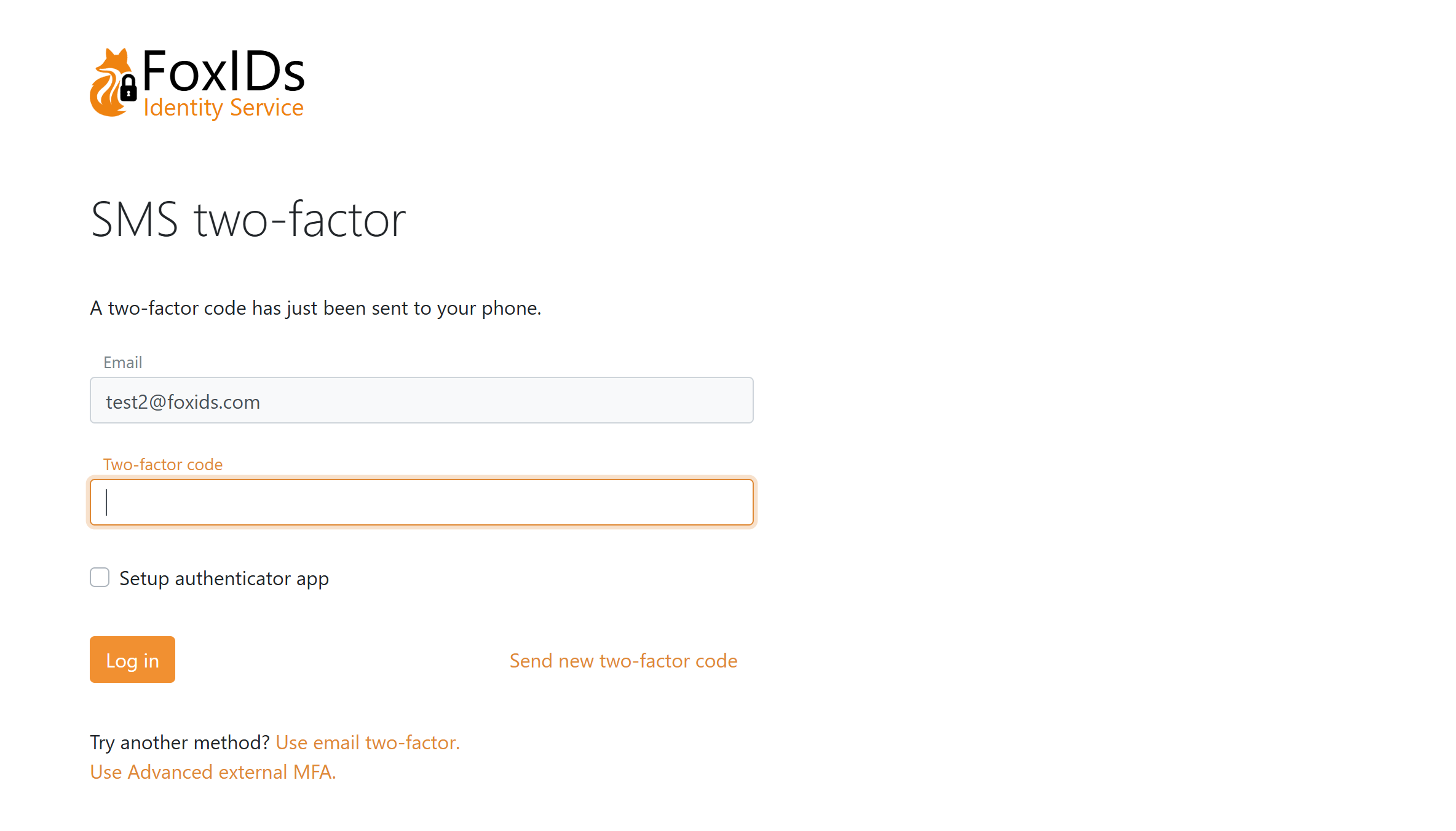
Página MFA SMS com registo opcional da app autenticadora e a opção de escolher um item MFA diferente.
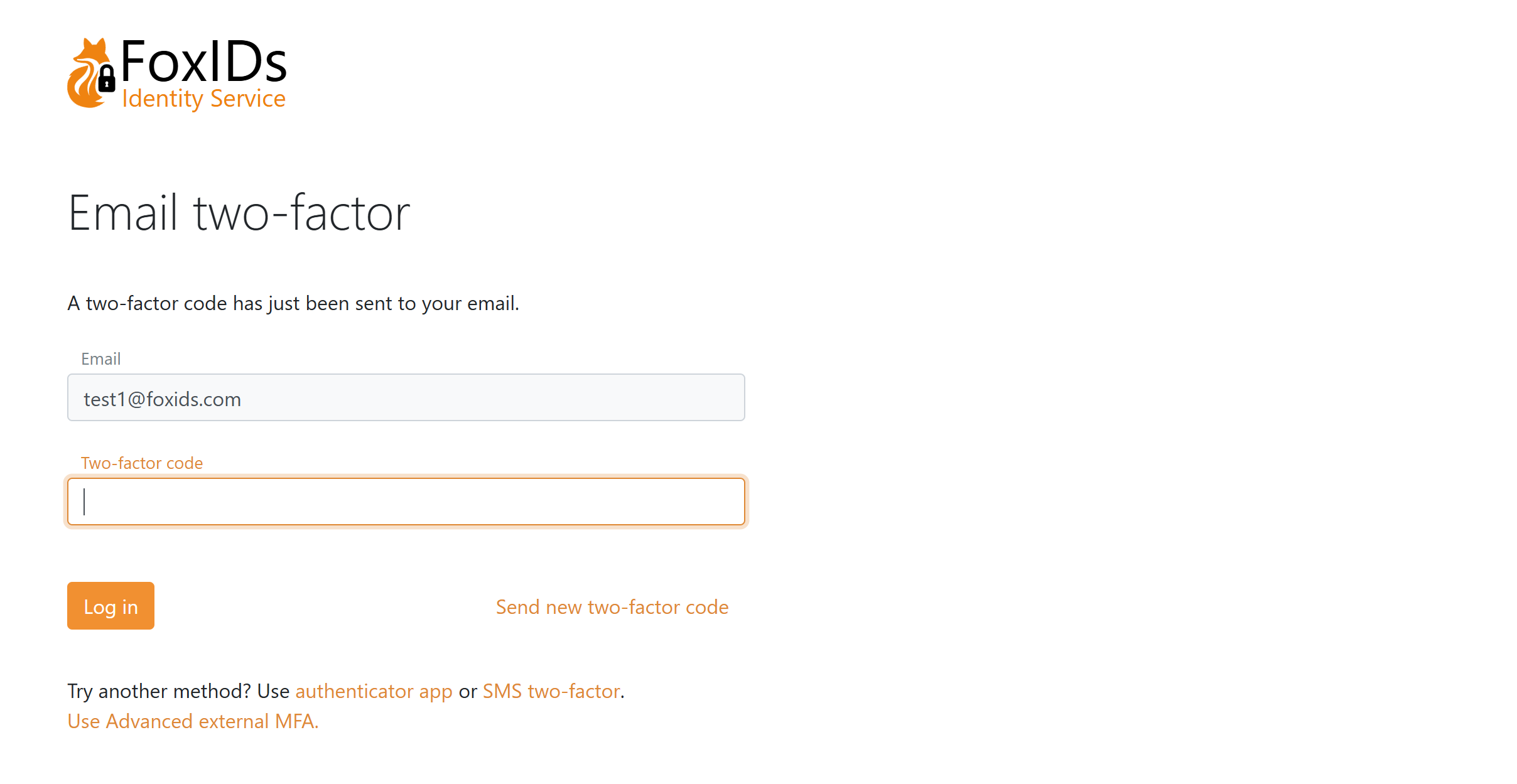
Página MFA email onde a app autenticadora é configurada, com a opção de escolher um item MFA diferente.
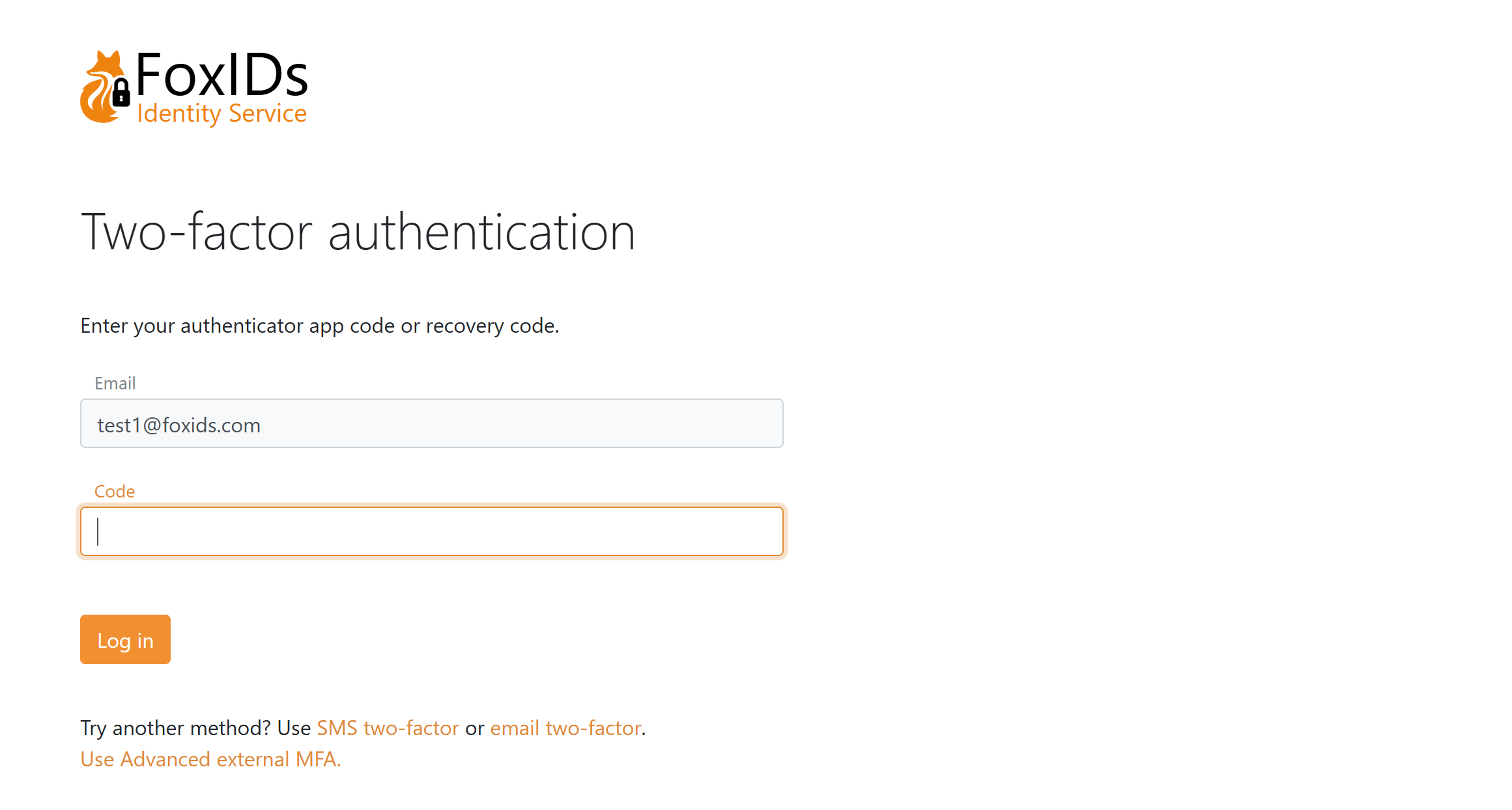
Página MFA app autenticadora com a opção de escolher um item MFA diferente.
Métodos de autenticação usados como itens MFA
Métodos de autenticação (OIDC, SAML 2.0, Environment Link) podem ser usados como itens MFA com estas regras:
- Valores ACR específicos de MFA não são encaminhados para o pedido do método de autenticação MFA.
- A resposta do método de autenticação tem de incluir o valor AMR exigido para o item MFA selecionado.
- O valor AMR é normalmente adicionado na transformação de claims se a identidade devolvida corresponder à identidade esperada. Veja o exemplo de transformação de claims.
- Se o valor AMR exigido estiver em falta, o login falha.
- Após validação com sucesso, o FoxIDs adiciona AMR
mfaà sessão resultante.
Pedir MFA a partir das aplicações
As aplicações podem pedir MFA tanto em OpenID Connect como em SAML 2.0.
Se forem pedidos valores ACR específicos, mas estes não estiverem configurados em itens MFA no método de autenticação de login selecionado, a autenticação falha.
OpenID Connect
Use acr_values:
- MFA geral:
acr_values=urn:foxids:mfa - MFA geral e método específico:
acr_values=urn:foxids:mfa urn:foxids:link
SAML 2.0
Use RequestedAuthnContext.AuthnContextClassRef:
- MFA geral: incluir
urn:foxids:mfa - MFA geral e método específico: incluir
urn:foxids:mfae valores específicos comourn:foxids:link
Comportamento da sessão
O FoxIDs valida os valores AMR exigidos face à sessão de login atual.
- Novo login: a sessão é criada depois de todos os requisitos serem cumpridos.
- Step-up login: uma sessão existente é atualizada depois de todos os requisitos MFA adicionais serem cumpridos.
- Reutilização de sessão: se a sessão já satisfizer os valores AMR exigidos, o FoxIDs reutiliza a sessão e não volta a pedir login.
Resolução de problemas
Razões comuns para falhas MFA:
- Os valores ACR pedidos não estão configurados como itens MFA no método de autenticação de login.
- Um método de autenticação usado como MFA não devolve o valor AMR exigido.
- Nenhum item MFA configurado está atualmente disponível para o utilizador, por exemplo porque faltam dados de telefone ou email para SMS ou email.